After that they had usage of Secure Wallet ??s program, they manipulated the consumer interface (UI) that purchasers like copyright workforce would see. They changed a benign JavaScript code with code made to change the intended location in the ETH inside the wallet to wallets controlled by North Korean operatives. This malicious code would only
 Danny Tamberelli Then & Now!
Danny Tamberelli Then & Now! Ben Savage Then & Now!
Ben Savage Then & Now! Andrea Barber Then & Now!
Andrea Barber Then & Now!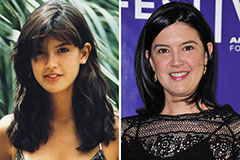 Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Mary Beth McDonough Then & Now!
Mary Beth McDonough Then & Now!